Free 3g Vpn Iphone And Free Cisco Vpn Client For Mac Os X. Description Additional Information Reviews(1). Download Free Cisco AnyConnect for Mac. If you looking on the internet a Cisco AnyConnect for Mac So, you come to the right place now a day shares with you an amazing application for Mac user it’s the best option to secure a web browser VPN can use in Mac Operating system and developed by Cisco Systems Corporation. You can not need any client end configurations.
- Cisco Anyconnect Vpn Client For Mac Os X Yosemite
- Vpn Client Cisco For Mac Os 10.12
- Vpn Client Cisco For Mac Os 10.7
- Download Vpn Client For Mac Os X
Follow the instructions below to download, install and connect the AnyConnect Secure Mobility Client on your Mac computer (OS X 10.9 or newer) to the new MSU VPN.
Instructions
Download:
- Go to https://www3.montana.edu/software.
Locate the Cisco AnyConnect (VPN Client) section (see image below). - Click box next to I accept Software Terms of Use.
- Click the AnyConnect Secure Mobility Client (4.8) download link in the Mac OS X row (shownin red below).
The installer file downloads. When download is complete, follow steps below to install.
Install client:
- Go to your Downloads folder (or whatever location the file was downloaded to) and double-click anyconnect-macos-4.8.00175-core-vpn-webdeploy-k9.dmg to unzip.
- Double-click anyconnect-macos-..pkg file to begin installation (see 1st image below).
The AnyConnect Secure Mobility Client Installer window opens (see 2nd image below). - Click Continue and follow the steps to install.
- Enter your computer's password when prompted.
- Click Close to shut installer window, after installation is finished.
- Click the Move to Trash button when prompted.
Installation will now be complete.
Connect to VPN:
- Go to your Applications folder, open the Cisco folder and then click the Cisco AnyConnect Secure Mobility Client. app.
The AnyConnect window opens (see image below). - Enter vpn.msu.montana.edu (if not already entered) and click Connect (see top image below).
In the login window that opens (see bottom image): - Select Group (appropriate for you role at MSU, ie MSU-Employee or MSU-Student).
- Enter NetID and NetID password, click OK.
You will now be connected to the MSU VPN. The Cisco icon in the dock will now have a little padlock on it and a tiny version Cisco round logo with padlock will be displayed on top menu bar.
To disconnect:
Right-click on the icon in top menu bar and select Disconnect.
To connect in the future:
You will no longer go through Network Preferences to connect to the VPN, just use the AnyConnect app.
Connect by right-clicking on the Cisco AnyConnect icon in the top menu bar or dock, then click the Connect button in the 'VPN Ready to connect' box.
If you don't see the icon in your top menu bar or dock, go to your Applications folder, open the Cisco folder and click the AnyConnect Secure Mobility Client.app. Next click the Connect button as shown in the image under step 4 above.
This article outlines instructions to configure a client VPN connection on commonly-used operating systems. For more information about client VPN, please refer to our Client VPN Overviewdocumentation.
For troubleshooting, please refer to our Troubleshooting Client VPN documentation.
Android
To configure an Android device to connect to the Client VPN, follow these steps:
- Navigate to Settings -> Wireless & Networks -> VPN
- Click the Plus Icon to add an additional VPN profile
Name: This can be anything you want to name this connection, for example, 'Work VPN.'
Type: select L2TP/IPSEC PSK
Server address: Enter the hostname (e.g. .com)orthe active WAN IP (e.g. XXX.XXX.XXX). Hostname is encouraged instead of active WAN IP because it is more reliable in cases of WAN failover. Admin can find them in Dashboard, under Security appliance > Monitor > Appliance status.
IPSec pre-shared key: Enter the pre-shared key that admin created in Security appliance >Configure > Client VPN settings.
Press save
You will be prompted for user credentials when you connect.
Chrome OS
Chrome OS based devices can be configured to connect to the Client VPN feature on MX Security Appliances. This allows remote users to securely connect to the LAN. This article will cover how to configure the VPN connection on a Chrome OS device. For more information on how to setup the Client VPN feature of the MX or how to connect from other operating systems, please visit the MX documentation.
- If you haven't already, sign in to your Chromebook.
- Click the status area at the bottom of your screen, where your account picture is located.
- Select Settings.
- In the 'Internet connection' section, click Add connection.
- Select Add private network.
- In the box that appears, fill in the information below:
- Server hostname:Enter the hostname (e.g. .com)orthe active WAN IP (e.g. XXX.XXX.XXX). Hostname is encouraged instead of active WAN IP because it is more reliable in cases of WAN failover. Admin can find them in Dashboard, under Security appliance > Monitor > Appliance status.
- Service name: This can be anything you want to name this connection, for example, 'Work VPN.'
- Provider type: Select L2TP/IPsec + Pre-shared key.
- Pre-shared key: Enter shared secret that admin created in Security appliance >Configure > Client VPN settings.
- Username credentials for connecting to VPN. If using Meraki authentication, this will be an e-mail address.
- Password credentials for connecting to VPN.
- Click Connect.
For more information regarding the configuration of VPN connections in Chrome OS, visit the Google Support page.
To configure an iOS device to connect to the Client VPN, follow these steps:
- Navigate to Settings -> General-> VPN -> Add VPN Configuration..
- Type: set to L2TP.
- Description:This can be anything you want to name this connection, for example, 'Work VPN.'
- Server: Enter the hostname (e.g. .com)orthe active WAN IP (e.g. XXX.XXX.XXX). Hostname is encouraged instead of active WAN IP because it is more reliable in cases of WAN failover. Admin can find them in Dashboard, under Security appliance > Monitor > Appliance status.
- Account: Enter the username
- Password: Enter if desired. If the password is left blank, it will need to be entered each time the device attempts to connect to the Client VPN.
- Secret: Enter shared secret that admin created in Security appliance >Configure > Client VPN settings.
- Ensure that Send All Traffic is set to On.
- Save the configuration.
macOS
Currently only the following authentication mechanisms are supported:

- User authentication: Active Directory (AD), RADIUS, or Meraki hosted authentication.
- Machine authentication: Preshared keys (a.k.a., shared secret).
When using Meraki hosted authentication, VPN account/user name setting on client devices (e.g., PC or Mac) is the user email address entered in the Dashboard.
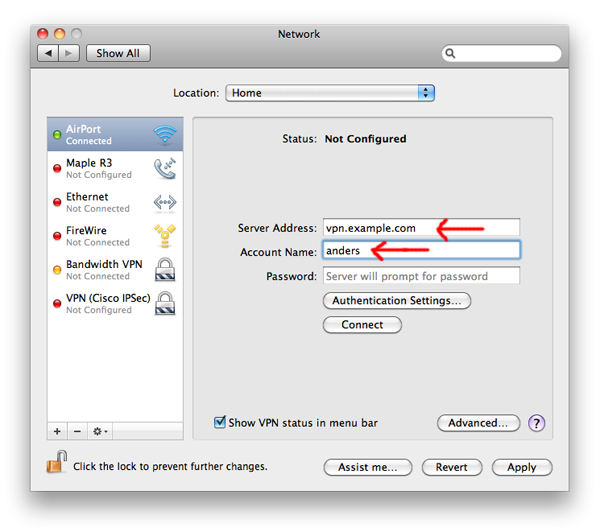
The instructions below are tested on Mac OS 10.7.3 (Lion).
Open System Preferences > Network from Mac applications menu. Click the '+' button to create a new service, then select VPN as the interface type, and choose L2TP over IPsec from the pull-down menu.
- Server Address: Enter the hostname (e.g. .com)orthe active WAN IP (e.g. XXX.XXX.XXX). Hostname is encouraged instead of active WAN IP because it is more reliable in cases of WAN failover. Admin can find them in Dashboard, under Security appliance > Monitor > Appliance status.
- Account Name: Enter the account name of the user (based on AD, RADIUS or Meraki Cloud authentication).
- User Authentication > Password: User password (based on AD, RADIUS or Meraki Cloud authentication).
- Machine Authentication > Shared Secret: Enter shared secret that admin created in Security appliance >Configure > Client VPN settings.
The VPN connectivity will not be established if you don't enable the Send all traffic over VPN connection option!
Windows 7
Currently only the following authentication mechanisms are supported:
- User authentication: Active Directory (AD), RADIUS, or Meraki hosted authentication.
- Machine authentication: Preshared keys (a.k.a., shared secret).
When using Meraki hosted authentication, VPN account/user name setting on client devices (e.g., PC or Mac) is the user email address entered in the Dashboard.
Open Start Menu > Control Panel, click on Network and Internet, click on View network status and tasks.
In the Set up a connection or network pop-up window, choose Connect to a workplace (Set up a dial-up or VPN connection to your workplace).
Choose Use my Internet connection (VPN), in the Connect to a workspace dialog window.
In the Connect to a Workplace dialog box, enter:
- Internet address: Enter the hostname (e.g. .com)orthe active WAN IP (e.g. XXX.XXX.XXX). Hostname is encouraged instead of active WAN IP because it is more reliable in cases of WAN failover. Admin can find them in Dashboard, under Security appliance > Monitor > Appliance status.
- Destination name:This can be anything you want to name this connection, for example, 'Work VPN.'
Choose 'Don't connect now; just set it up so that I can connect later' option.
With the advent of 4K, an increasing number of devices start to deliver 4K resolution, like YouTube 4K smart video, 4K TV, Apple’s 27-inch iMac, iPhone 6s, etc.But not all computers support the smooth playback of 4K videos. If you want to watch 4K videos on your Mac, you’d better get a Mac 4K player installed firstly.The can help you play 4K Ultra HD movies in any format with the highest picture quality and accuracy delivered. 4K means more pixels, clearer image, more details on the screen than 1080P standard HD. Youtube player for mac.
Click Next. In the next dialog window, enter the user credentials, and click Create.

Despite the name 'Unencrypted PAP', the client's password is sent encrypted over an IPsec tunnel between the client device and the MX. The password is fully secure and never sent in clear text over either the WAN or the LAN.
Windows 8
Currently only the following authentication mechanisms are supported:
- User authentication: Active Directory (AD), RADIUS, or Meraki hosted authentication.
- Machine authentication: Preshared keys (a.k.a., shared secret).
When using Meraki hosted authentication, VPN account/user name setting on client devices (e.g., PC or Mac) is the user email address entered in the Dashboard.
Open Start Menu > Network and Sharing Center and click Settings.
In the Set Up a Connection or Network pop-up window, choose Connect to a workplace.
(Set up a dial-up or VPN connection to your workplace).
Choose Use my Internet connection (VPN), in the Connect to a Workspace dialog window.
In the Connect to a Workplace dialog box, enter:
- Internet address: Enter the hostname (e.g. .com)orthe active WAN IP (e.g. XXX.XXX.XXX). Hostname is encouraged instead of active WAN IP because it is more reliable in cases of WAN failover. Admin can find them in Dashboard, under Security appliance > Monitor > Appliance status.
- Destination name:This can be anything you want to name this connection, for example, 'Work VPN.'
Cisco Anyconnect Vpn Client For Mac Os X Yosemite
Go back to Network and Sharing Center and click Change Adapter Settings.
Despite the name 'Unencrypted PAP', the client's password is sent encrypted over an IPsec tunnel between the client device and the MX. The password is fully secure and never sent in clear text over either the WAN or the LAN.
Windows 10
Currently only the following authentication mechanisms are supported:
- User authentication: Active Directory (AD), RADIUS, or Meraki hosted authentication.
- Machine authentication: Preshared keys (a.k.a., shared secret).
When using Meraki hosted authentication, VPN account/user name setting on client devices (e.g., PC or Mac) is the user email address entered in the Dashboard.
Open Start Menu > Search 'VPN' > Click Change virtual private networks (VPN)
From the VPN settings page, click Add a VPN connection.
In the Add a VPN connection dialog:
- VPN provider: Set to Windows (built-in)
- Connection name: This can be anything you want to name this connection, for example, 'Work VPN.'
- Server name or address: Enter the hostname (e.g. .com)orthe active WAN IP (e.g. XXX.XXX.XXX). Hostname is encouraged instead of active WAN IP because it is more reliable in cases of WAN failover. Admin can find them in Dashboard, under Security appliance > Monitor > Appliance status.
- VPN type: Select L2TP/IPsec with pre-shared key
- User name and Password: optional
Press Save.
What are my options?Although you'll still be able to use Office 2016 for Mac, you will no longer receive security updates and bug fixes after October 13, 2020. Upgrade to a newer version of Office so you can stay up to date with all the latest features, patches, and security updates.Upgrade options include:.Recommended: Upgrade to Microsoft 365, the subscription version of Office that comes with Word, Excel, PowerPoint, and other apps, depending on the plan you choose. Microsoft office for mac one time purchase. With Microsoft 365, the apps are available on your computer and via browser; one subscription enables you to use them on both your Mac and PC. This lifecycle typically lasts for 5 years from the date of the product’s initial release.For more information about the support lifecycle for Microsoft products, see. In fact, most online help content will be retired.Why is Microsoft doing this?Office 2016 for Mac, like most Microsoft products, has a support lifecycle during which we provide new features, bug fixes, security fixes, and so on.
After the VPN connection has been created, click Change adapter options under Related settings.
Right-click on the VPN Connection from the list of adapters and click Properties.
Despite the name 'Unencrypted PAP', the client's password is sent encrypted over an IPsec tunnel between the client device and the MX. The password is fully secure and never sent in clear text over either the WAN or the LAN.
In Advanced Properties dialog box, choose 'Use preshared key for authentication' and enter the pre-shared key that admin created in Security appliance >Configure > Client VPN settings.

Vpn Client Cisco For Mac Os 10.12
Back at the Network Connections window, right-click on the VPN connection and click Connect / Disconnect.
Find your VPN profile and click Connect.
Vpn Client Cisco For Mac Os 10.7
Windows XP
Currently only the following authentication mechanisms are supported:
- User authentication: Active Directory (AD), RADIUS, or Meraki hosted authentication.
- Machine authentication: Preshared keys (a.k.a., shared secret).
When using Meraki hosted authentication, use the email address for VPN account / user name.
Open Start Menu > Control Panel, click on Network Connections.
In the Network Tasks section, click on Create a new connection.
Choose Connect to the network at my workplace, in the New Connection Wizard window.
Choose Virtual Private Network connection in the next section.
Then, give a name for this connection. This can be anything you want to name this connection, for example, 'Work VPN.'
Enter the hostname (e.g. .com)orthe active WAN IP (e.g. XXX.XXX.XXX). Hostname is encouraged instead of active WAN IP because it is more reliable in cases of WAN failover. Admin can find them in Dashboard, under Security appliance > Monitor > Appliance status.
In the Connect <Connection Name> box, click on Properties
Download Vpn Client For Mac Os X
In the General tab, verify the hostname (e.g. .com)orthe active WAN IP (e.g. XXX.XXX.XXX). Hostname is encouraged instead of active WAN IP because it is more reliable in cases of WAN failover. Admin can find them in Dashboard, under Security appliance > Monitor > Appliance status.

Despite the name 'Unencrypted PAP', the client's password is sent encrypted over an IPsec tunnel between the client device and the MX. The password is fully secure and never sent in clear text over either the WAN or the LAN.
Linux
Since Client VPN uses the L2TP over IPsec standard, any Linux client that properly supports this standard should suffice. Please note that newer versions of Ubuntu do not ship with a VPN client that supports L2TP/IP, and will therefore require a 3rd party VPN client that supports the protocol.
Note: The xl2tp package does not send user credentials properly to the MX when using Meraki Cloud Controller authentication, and this causes the authentication request to fail. Active Directory or RADIUS authentication can be used instead for successful authentication.